Log Data Security and Anti-Tampering Design Guide
A comprehensive framework for building trustworthy, tamper-evident, and legally defensible log evidence chains — from event generation through immutable storage, integrity verification, and forensic export.
System Overview
This guide treats logs as a digital evidence chain rather than mere operational telemetry. The core goal is to ensure that logs remain trustworthy, complete, time-consistent, and legally defensible from the moment an event occurs until the moment a security analyst, auditor, or forensic investigator uses it. The design philosophy is grounded in the principle that evidence must be immutable, while search and analysis are convenience layers built on top of that immutable foundation.
The system scope encompasses seven functional layers: (1) log generation sources including OS/applications, identity systems, databases, endpoints, network/security devices, and cloud audit trails; (2) collection and forwarding layers with local buffering and reliable delivery; (3) transmission security via mutual TLS and VPN; (4) centralized storage with raw/index separation; (5) integrity protection and immutability controls using hash chains and WORM storage; (6) role-based access with separation of duties; and (7) auditability and evidence export with chain-of-custody records.
Target Scale
2,000–50,000 EPS across mixed sources: servers, AD/IdP, EDR, firewall, WAF, IDS/IPS, and cloud audit trails.
Retention Policy
Hot searchable: 30–180 days. Warm/archive: 1–7 years depending on regulatory requirements.
Compliance Baseline
ISO/IEC 27001 controls, SOC 2-style evidence, log retention + integrity + access audit requirements.
In-Scope Outputs
- Normalized events to SIEM/search
- Raw logs preserved in immutable form
- Integrity verification reports
- Retention and lifecycle reports
- Privileged access audit trails
- Evidence export packages with hash manifests
Out of Scope
- Full packet capture as log replacement
- Deep endpoint telemetry beyond retention policy
- Altering source systems' native audit logs
- Vulnerability management (consumes logs only)
- EDR platform management (consumes logs only)
Key Dependencies
The system depends on several foundational infrastructure components that must be in place before deployment. These dependencies are not optional — their absence or misconfiguration directly impacts the integrity and trustworthiness of the evidence chain.
System Architecture
The evidence-chain logging architecture is organized into five functional layers, each with distinct responsibilities and security boundaries. Data flows from left to right through the layers, while control signals — including keys, policies, time synchronization, and privileged operation approvals — flow vertically from the governance infrastructure to all layers. The Raw Log Vault sits at the center of the evidence model: all other components are designed to protect, verify, and provide controlled access to the immutable evidence stored within it.
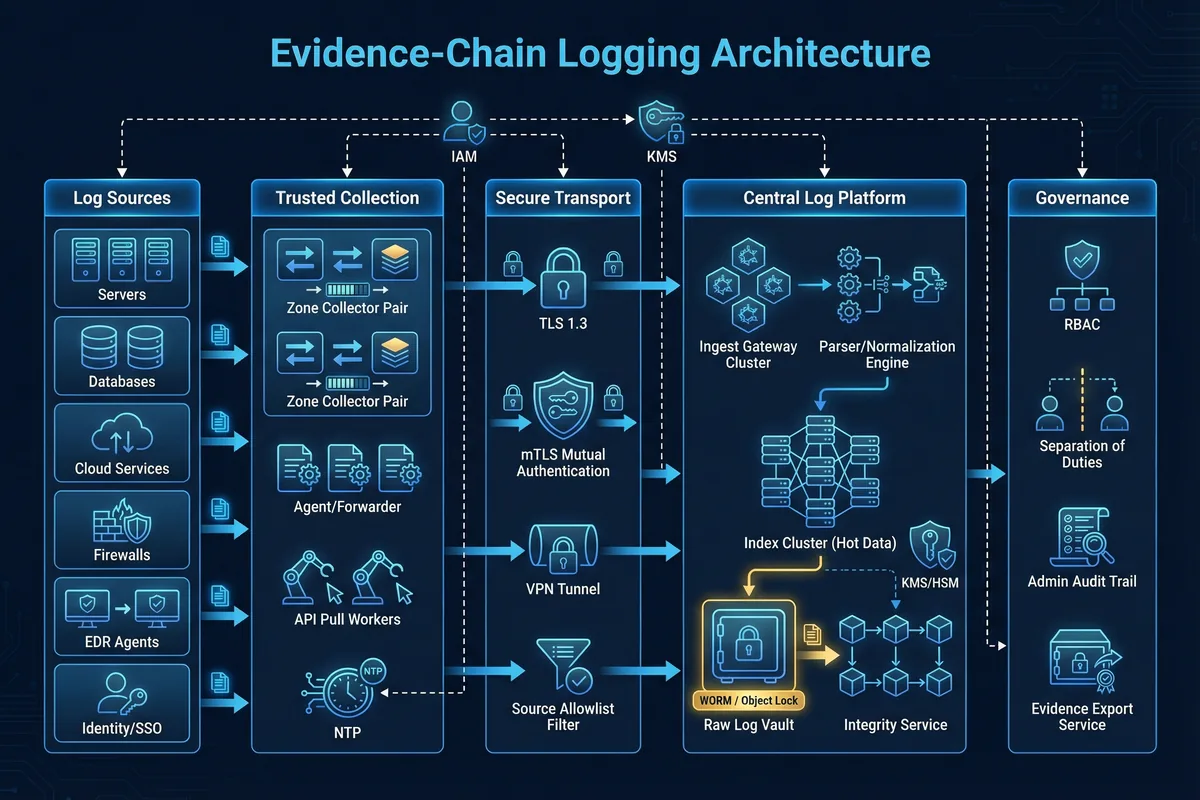
The five layers serve distinct roles in the evidence chain. The Log Sources layer generates audit records and enforces local audit policies. The Trusted Collection layer provides reliable delivery with buffering, retry, and identity binding. The Secure Transport layer encrypts, authenticates, and constrains who can send logs. The Central Log Platform separates raw evidence storage from the query index, applies integrity mechanisms, and enforces immutability. The Governance layer enforces least privilege, dual control for high-risk actions, and complete administrative auditability.
| Layer | Primary Responsibility | Key Security Control | Failure Impact |
|---|---|---|---|
| Log Sources | Generate events; enforce audit policy | Local audit config; log buffer protection | Missing critical fields; disabled audit categories |
| Trusted Collection | Buffer, retry, identity binding, time normalization | Device certs; local queue; dual timestamps | Silent loss during outage; spoofed sources |
| Secure Transport | Encrypt, authenticate, constrain senders | mTLS; source allowlist; VPN/leased line | Log injection; eavesdropping; replay attacks |
| Central Log Platform | Raw evidence + index separation; integrity | WORM/Object Lock; hash chain; KMS | Tampered evidence; undetected deletion |
| Governance | Least privilege; dual control; auditability | RBAC/SoD; immutable admin audit store | Insider purge; unaccountable admin actions |
Major Functions
The system implements six core functions that together form a closed-loop evidence chain. Each function is designed with specific implementation requirements and acceptance criteria to ensure the system meets its security and compliance objectives. The circular dependency between these functions means that weakening any single function degrades the trustworthiness of the entire evidence chain.

1. Trusted Collection & Reliable Delivery
Local buffering, backpressure control, replay protection. Acceptance: forced network outage test shows no silent loss beyond defined buffer capacity.
2. Time Consistency
Unified time source; detect clock drift; record both event time and receive time. Acceptance: drift alarms trigger when skew exceeds threshold.
3. Encrypted & Authenticated Transport
TLS/mTLS, VPN/leased line, source allowlist, cert rotation. Acceptance: reject unauthenticated sender; cipher suite meets policy.
4. Centralized Storage with Raw/Index Separation
Raw logs go to immutable vault; index is rebuildable. Acceptance: index deletion does not remove raw evidence; rebuild procedure works.
5. Integrity Protection & Anti-Tampering
Hash chains, digital signatures, periodic verification, immutable storage locks. Acceptance: any modification attempt is detected; verification report produced on schedule.
6. Permission Isolation & Traceable Operations
Least privilege, separation of duties, dual approval for destructive actions. Acceptance: operator cannot delete/alter raw logs; admin actions are fully auditable.
Chapter Navigation
This guide is organized into twelve chapters, each addressing a distinct aspect of log data security and anti-tampering design. Navigate directly to any chapter using the cards below or the sidebar navigation.