Chapter 7: Support & Integration
Supporting infrastructure requirements, third-party integrations, and ecosystem compatibility
7.1 Integrated Supporting Equipment
A log security system does not operate in isolation — it depends on a set of supporting infrastructure components that must be correctly configured and maintained to ensure the integrity of the evidence chain. The diagram below shows all supporting equipment categories integrated into a single view, illustrating the data flows and dependencies between each component and the central log security platform.
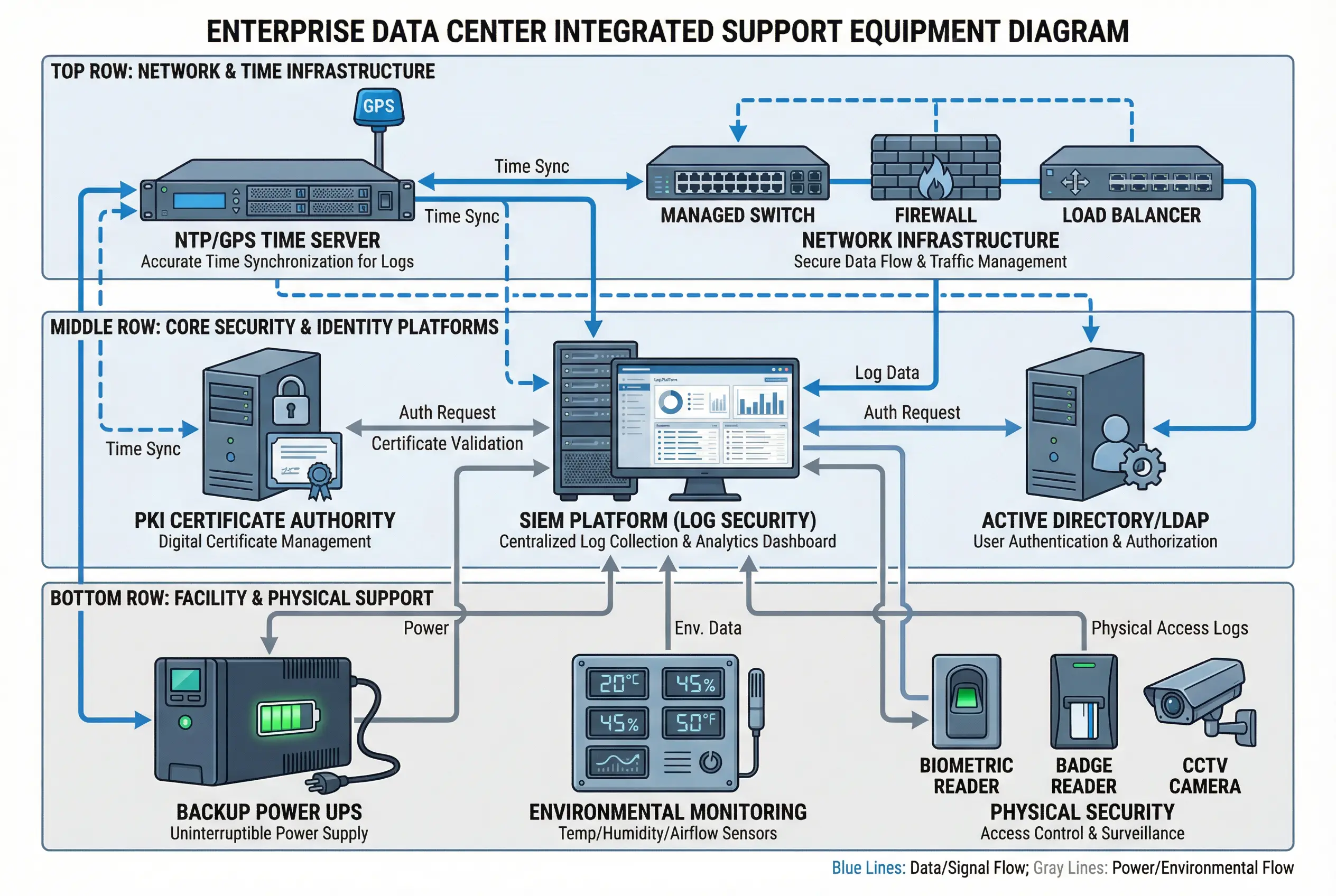
The diagram organizes supporting equipment into three functional rows. The top row covers network and time infrastructure, which provides the foundational connectivity and time synchronization that all other components depend on. The middle row covers core security and identity platforms, which provide authentication, authorization, and log analytics capabilities. The bottom row covers facility and physical support, which ensures the availability and physical security of the log security system hardware. All three rows are interconnected through the central SIEM Platform, which acts as the integration hub.
7.2 Supporting Equipment Requirements
The table below specifies the minimum requirements for each supporting equipment category, including the integration method, the criticality to the evidence chain, and the failure mode if the component is unavailable.
| Component | Integration Method | Criticality | Failure Mode | Redundancy Requirement |
|---|---|---|---|---|
| NTP/GPS Time Server | NTP v4 (authenticated) | Critical | Timestamp drift; hash chain gaps | 2× servers (primary + backup) |
| Managed Switch | Physical layer; VLAN tagging | Critical | Log transport failure; complete outage | Stacked pair or MLAG |
| Firewall | Zone boundary enforcement | Critical | Zone isolation failure; unauthorized access | Active-passive HA pair |
| Load Balancer | VIP for ingest gateway cluster | High | Single gateway becomes bottleneck | Active-active pair |
| PKI / Certificate Authority | PKCS#11 / SCEP / EST | Critical | mTLS certificate renewal failure | Offline root CA + online issuing CA |
| Active Directory / LDAP | LDAPS / Kerberos | High | RBAC enforcement failure; access control gap | Multi-DC replication |
| SIEM Platform | Elasticsearch / OpenSearch API | High | Search unavailable; analyst access blocked | 3-node cluster minimum |
| UPS / Generator | SNMP monitoring | Critical | Power failure causes log loss and data corruption | UPS + generator for >4h runtime |
| Environmental Monitoring | SNMP / REST API | Medium | Undetected overheating causes hardware failure | Redundant sensors per zone |
| Physical Security (Biometric/CCTV) | Access control API / RTSP | High | Unauthorized physical access undetected | Battery backup for access control |
7.3 Third-Party Integration Points
The log security system exposes a set of well-defined integration points for third-party platforms. Each integration point uses a standard protocol or API to ensure interoperability with the broadest range of vendor products. The following integration categories are supported out of the box, with additional integrations available through the REST API.
SIEM / SOAR Platforms
Normalized events are forwarded to SIEM platforms (Splunk, IBM QRadar, Microsoft Sentinel, Elastic SIEM) via CEF/LEEF syslog or native API. SOAR platforms (Palo Alto XSOAR, Splunk SOAR) can trigger automated playbooks based on integrity alerts. The integration uses read-only API keys scoped to specific log namespaces.
Identity & Access Management
RBAC is enforced through integration with Active Directory / LDAP (LDAPS/Kerberos) or SAML 2.0 / OIDC identity providers (Okta, Azure AD, Ping Identity). Role assignments are synchronized automatically from the IdP, and access reviews are triggered via the SCIM provisioning API. MFA enforcement is delegated to the IdP.
PKI & Certificate Management
TLS certificates for all system components are issued by the organization's PKI. Automated certificate lifecycle management is supported via SCEP (for network devices), EST (RFC 7030), and ACME (for cloud deployments). Certificate expiry monitoring is integrated with the alerting system to provide 90/30/7-day advance warnings.
Monitoring & Alerting
System health metrics are exported via Prometheus (for Grafana dashboards) or SNMP (for legacy NMS platforms). Alerts are delivered via PagerDuty, OpsGenie, or email/SMS. The alerting system supports escalation policies with configurable thresholds for EPS drop, buffer fill level, hash chain gaps, and certificate expiry.
Ticketing & GRC Platforms
Compliance reports and integrity verification results can be automatically pushed to GRC platforms (ServiceNow GRC, Archer, MetricStream) via REST API. Integrity failure alerts automatically create incidents in ITSM platforms (ServiceNow, Jira Service Management) with pre-populated evidence packages. Audit evidence packages are formatted for direct upload to compliance portals.