Chapter 5: Selection & Interfaces
Core product introduction, interface logic, connection diagrams, and feature comparison tables
5.1 Core Product Introduction
The log security system is composed of five core hardware and software product categories, each addressing a specific layer of the evidence chain. Product selection within each category should be driven by the capacity requirements established in Chapter 4, the compliance requirements identified in Chapter 3, and the interface compatibility requirements described in Section 5.2. The product overview image below shows the five core product categories in their typical physical form factors.

1. Log Collector Pro Series
The Log Collector Pro Series is a purpose-built appliance for log collection, buffering, and secure forwarding. It supports multiple input protocols (syslog/TLS, Beats, Fluentd, Windows Event Forwarding) and provides local disk buffering for store-and-forward operation during network outages. The appliance includes a TPM 2.0 chip for device identity binding and supports certificate-based mutual TLS authentication to the ingest gateway.
2. HSM-2000 Hardware Security Module
The HSM-2000 provides FIPS 140-2 Level 3 certified key management for the log security system. It stores master keys for log encryption, signing keys for hash chain signatures, and key encryption keys for the KMS hierarchy. The HSM enforces dual-control key ceremonies and provides tamper-evident physical protection. All key operations are logged to an immutable internal audit store that cannot be cleared even by the HSM administrator.
3. Vault Storage Array
The Vault Storage Array provides the physical storage layer for the Raw Log Vault. It supports WORM (Write Once Read Many) retention locks at the storage platform level, ensuring that immutability cannot be bypassed by software-level commands. The array supports both SnapLock (NetApp-compatible) and S3 Object Lock API modes, allowing integration with both on-premises and cloud-native architectures. Dual-parity RAID with hot spares ensures data durability during drive failures.
4. Ingest Gateway Appliance
The Ingest Gateway terminates mTLS connections from zone collectors, enforces the source allowlist, applies rate limiting, and routes log segments to the message queue. It is designed to be stateless and horizontally scalable — multiple gateway instances can be deployed behind a load balancer without coordination. The gateway validates the client certificate CN/SAN against the allowlist on every connection and rejects any sender not explicitly authorized.
5. Integrity Engine
The Integrity Engine maintains the hash chain across all stored log segments, produces signed verification manifests, and runs scheduled verification jobs to detect any tampering or corruption. It uses SHA-256 for segment hashes and ECDSA P-384 for manifest signatures, with signing keys stored in the HSM-2000. The front-panel display shows real-time verification status, allowing operators to confirm integrity without logging into the management interface.
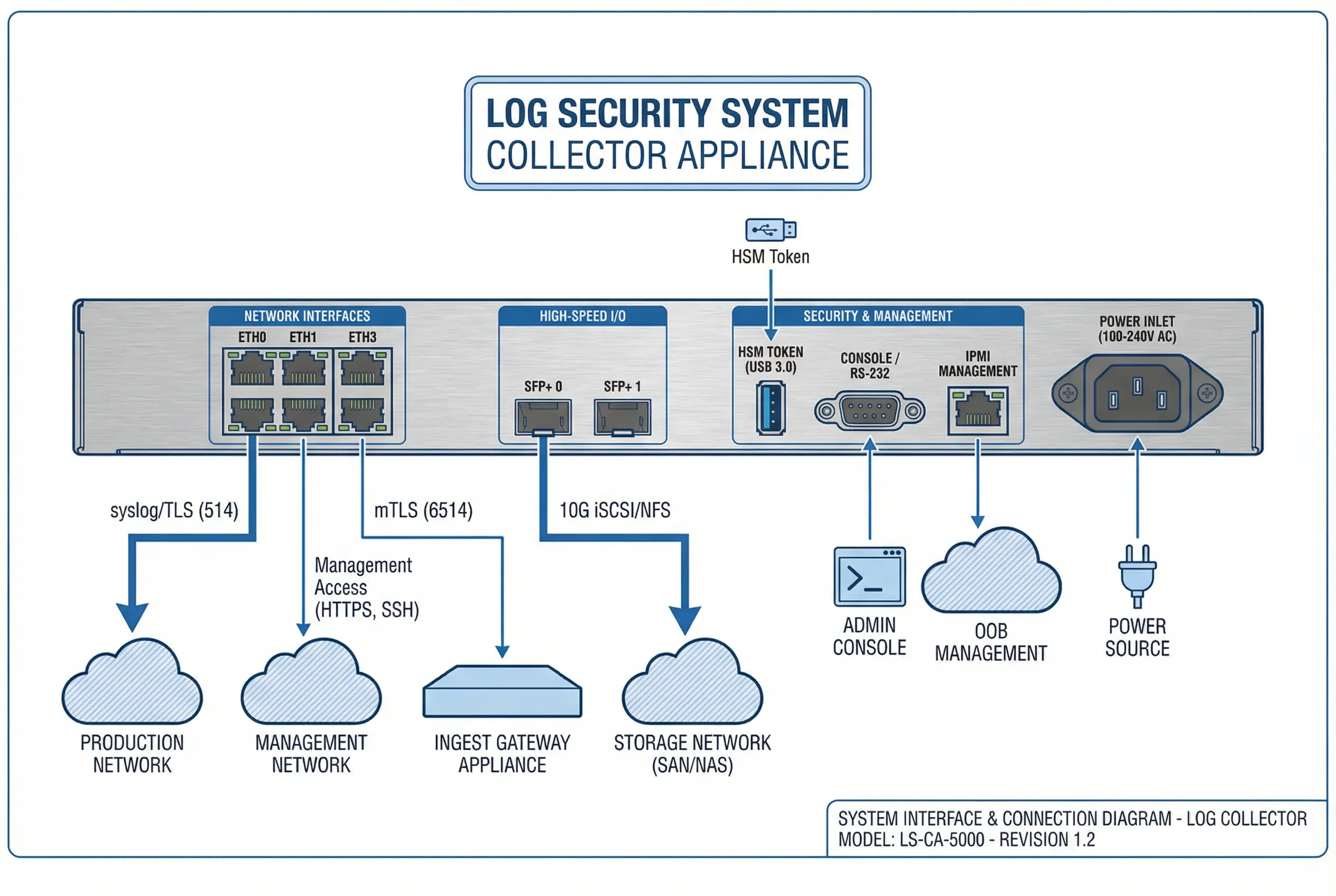
5.2 Typical Interface and Connection Logic
The interface diagram below shows the rear panel of the Log Collector Pro Series appliance with all physical ports labeled and their logical connections to the network infrastructure. Understanding the interface layout is essential for correct cabling, firewall rule configuration, and network segmentation. Each interface serves a distinct security function and must be connected to the appropriate network segment.
| Interface | Type | Protocol / Port | Connected To | Direction | Security Notes |
|---|---|---|---|---|---|
| ETH0 | GbE RJ45 | Syslog/TLS 514, Beats 5044 | Production Network | Inbound only | Allowlist source IPs; no outbound to production |
| ETH1 | GbE RJ45 | HTTPS 443, SSH 22 | Management Network | Bidirectional | Restrict to admin VLAN; MFA required |
| ETH2 | GbE RJ45 | mTLS 6514 | Ingest Gateway | Outbound only | Client cert required; no inbound from SecOps |
| ETH3 | GbE RJ45 | NTP 123 | NTP Server | Outbound only | Authenticated NTP; monitor drift |
| SFP+0 | 10G Fiber | iSCSI 3260 / NFS 2049 | Storage Network | Bidirectional | Dedicated storage VLAN; no routing to other zones |
| SFP+1 | 10G Fiber | Reserved for HA heartbeat | Collector B (peer) | Bidirectional | Dedicated HA VLAN; not routable |
| USB 3.0 | USB-A | PKCS#11 | HSM Token | Local only | Physical HSM token for signing key access |
| Console | RS-232 DB9 | Serial console | Console server | Bidirectional | Out-of-band access; requires physical presence |
| IPMI | GbE RJ45 | IPMI 623, HTTPS 443 | OOB Management Switch | Bidirectional | Separate OOB network; change default credentials |
5.3 Core Product Function Table
The function table below provides a comprehensive comparison of all five core products across the key functional dimensions of the evidence chain. Each cell indicates whether the product provides the function natively (Native), requires configuration (Config), depends on integration with another product (Integration), or does not provide the function (—). This table is intended to guide procurement decisions and integration planning.
| Function | Log Collector Pro | HSM-2000 | Vault Storage Array | Ingest Gateway | Integrity Engine |
|---|---|---|---|---|---|
| Multi-protocol input (syslog/Beats/WEF) | Native | — | — | — | — |
| Local disk buffering (store-and-forward) | Native | — | — | — | — |
| mTLS client authentication | Native | Integration | — | Native | — |
| Source allowlist enforcement | Config | — | — | Native | — |
| Rate limiting per source | — | — | — | Native | — |
| WORM / Object Lock storage | — | — | Native | — | — |
| AES-256 encryption at rest | Config | Integration | Native | — | — |
| Hash chain maintenance | — | — | — | — | Native |
| Digital signature (ECDSA) | — | Native | — | — | Integration |
| Scheduled integrity verification | — | — | — | — | Native |
| FIPS 140-2 Level 3 key protection | — | Native | — | — | — |
| Dual-control key ceremony | — | Native | — | — | — |
| TPM device identity binding | Native | — | — | — | — |
| NTP drift monitoring | Native | — | — | — | — |
| Evidence export with hash manifest | — | — | Config | — | Native |
| Immutable admin audit log | — | Native | Config | Config | Config |
| REST API for integration | Native | Native | Native | Native | Native |